Ubuntu is thwarting Microsoft’s efforts to keep PCs safe. Modern Windows PCs are required to ship with Secure Boot enabled, a safety measure that limits access to Microsoft-approved operating systems. To make life easier for Linux users, Microsoft provides Linux distribution bootloaders with a Microsoft signing key. But Ubuntu’s signed bootloader will happily boot unsigned code, breaking the whole chain of trust. Thankfully, this is set to change with the upcomingUbuntu 16.04 LTS.
Ubuntu’s Secure Boot support is not secure
Secure Boot is supposed to establish a chain of trust from the UEFI firmware all the way to the operating system. For example, when it’s used with Windows, the UEFI firmware ensures that the Windows bootloader bears a correct signing key that hasn’t been modified. The Windows bootloader then hands off to the next stage, which also checks for legitimacy. The goal is to ensure no rootkits have interfered with the boot process.
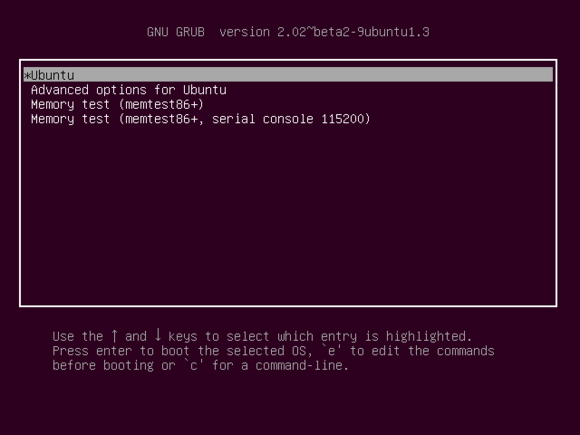
Linux distributions, for their part, have a signed bootloader from Microsoft, which gives them the go-ahead from the UEFI firmware. But with Ubuntu, once the UEFI firmware hands off, the bootloader doesn’t check to ensure that the Linux kernels it boots are signed by Canonical (maker of Ubuntu). Not only does this mean Secure Boot isn’t a security feature for Ubuntu users, it also means that a hacker could actually use Ubuntu’s trusted bootloader to boot untrusted malware on almost any Secure Boot-enabled PC: The Grub bootloader used by Ubuntu has a way to boot Windows, making it possible to attack Secure Boot-enabled Windows systems.
This isn’t common knowledge, but it’s not something Canonical hid, either. In a comment on a bug report from mid-2015, Ubuntu security engineer Marc Deslauriers wrote, “Ubuntu’s support for secure boot is solely intended as a compatibility measure so that media can boot on secure boot enabled computers. There are no current plans to enable secure boot as a security measure.”
Prominent free-software developer Matthew Garrett discovered this on January 6, 2016. In a series of profanity-laced tweets, he accused Ubuntu of “criminal ineptitude.” Noting the potential for the signed-by-Microsoft bootloader to be repurposed to attack other operating systems, Garrett added in a tweet. “This isn’t a decision that affects just Ubuntu users—*everybody* who uses UEFI Secure Boot has their security weakened by this.”
Ubuntu 16.04 should fix things
Despite its casual acknowledgement of the security vulnerability, Canonical is working on securing its Secure Boot implementation. As the Secure Boot page on Ubuntu’s wiki says:
“Canonical’s Secure Boot implementation in Ubuntu 15.10 and early [sic] is primarily about hardware-enablement," said Canonical. "If you want to use Secure Boot as a security mechanism, an appropriate solution would be to use your own keys (optionally enrolling additional keys, see above) and update the bootloader to prohibit booting an unsigned kernel. Ubuntu 16.04 LTS is planned to enable enforcing secure boot (see LP: #1401532 for details).”
Ubuntu 16.04 is scheduled for April 2016 release, giving Canonical just a few more months to reconfigure the bootloader with security in mind. However, as Garrett points out, those old Ubuntu bootloaders would also need to be blacklisted. They’re currently floating around out there, posing a potential security risk to the Secure Boot ecosystem.
It’s a shame, too. Secure Boot is a mandatory hardware feature for Windows 10-certified PCs, and PC manufacturers don’t have to include the signing key Microsoft provides for Linux distributions. If those signed Linux bootloaders represent a potential security threat, it could give Microsoft and PC manufacturers a reason to stop making things easy for Linux users.



ثبت نظر