یوتیوب به سازندگان محتوا دربارهی کلاهبرداری فیشینگ جدیدی که از ویدئوی تقلبی نیل موهان، مدیرعامل یوتیوب استفاده میکند،…
بیشتر بخوانیدیوتیوب دربارهی سوءاستفاده از ویدئوی جعلی مدیرعامل این پلتفرم هشدار داد
یوتیوب به سازندگان محتوا دربارهی کلاهبرداری فیشینگ جدیدی که از ویدئوی تقلبی نی… بیشتر بخوانید
 سهشنبه, 11 دی 1403
سهشنبه, 11 دی 1403
نفوذ گروه هکری چینی به وزارت خزانهداری آمریکا؛ رخنهای گسترده و بحثبرانگیز
بهتازگی گزارشهایی منتشر شده که نشان میدهد گروهی هکری تحت حمایت دولت چین موفق… بیشتر بخوانید
 دوشنبه, 28 آبان 1403
دوشنبه, 28 آبان 1403
حمله سایبری گسترده به T-Mobile آمریکا؛ نفوذ هکرهای چینی قطعی است
در یک رویداد امنیتی مهم، گزارشها حاکی از آن است که هکرهای چینی موفق به نفوذ به… بیشتر بخوانید
 دوشنبه, 16 مهر 1403
دوشنبه, 16 مهر 1403
سازمان ملل؛ تلگرام، پلتفرمی برای خرید و فروش اطلاعات شخصی و کالاهای قاچاق
سازمان ملل اعلام کرده است که پلتفرم پیامرسان تلگرام به یکی از ابزارهای مورد اس… بیشتر بخوانید

تکنولوژی و فناوری
نفوذ گروه هکری چینی به وزارت خزانهداری آمریکا؛ رخنهای گسترده و بحثبرانگیز
- تکنولوژی و فناوری
- علی احمدی
- سهشنبه, 11 دی 1403
بهتازگی گزارشهایی منتشر شده که نشان میدهد گروهی هکری تحت حمایت دولت چین موفق شدهاند به وزارت خزانهداری ایالات متحد…
بیشتر بخوانیدحمله سایبری گسترده به T-Mobile آمریکا؛ نفوذ هکرهای چینی قطعی است
- تکنولوژی و فناوری
- پویان معصومی
- دوشنبه, 28 آبان 1403
در یک رویداد امنیتی مهم، گزارشها حاکی از آن است که هکرهای چینی موفق به نفوذ به شبکه مخابراتی T-Mobile آمریکا شدهاند.
بیشتر بخوانیدسازمان ملل؛ تلگرام، پلتفرمی برای خرید و فروش اطلاعات شخصی و کالاهای قاچاق
- تکنولوژی و فناوری
- پویان معصومی
- دوشنبه, 16 مهر 1403
سازمان ملل اعلام کرده است که پلتفرم پیامرسان تلگرام به یکی از ابزارهای مورد استفاده مجرمان برای انجام فعالیتهای غیرقا…
بیشتر بخوانیدفاجعه بهروزرسانی CrowdStrike؛ اختلال در ۸٫۵ میلیون دستگاه ویندوزی
- تکنولوژی و فناوری
- پویان معصومی
- یکشنبه, 31 تیر 1403
روز جمعه، بهروزرسانی معیوب شرکت CrowdStrike موجب اختلال در ۸٫۵ میلیون کامپیوتر ویندوزی در سراسر جهان شد و هزاران کسبو…
بیشتر بخوانیدراهی باز و جذاب برای استارتاپها با هدف جلوگیری از قطعی گسترده
- تکنولوژی و فناوری
- مریم محمودی
- یکشنبه, 31 تیر 1403
نقص در بهروزرسانی CrowdStrike، زنگ خطری برای وابستگی به نرمافزارهای معیوب و فرصتی برای نوآوری در امنیت سایبری است.
بیشتر بخوانیدکسپرسکی اعلام میکند که پیچیدهترین حمله سایبری به آیفون کشف شده است
- تکنولوژی و فناوری
- پویان معصومی
- جمعه, 08 دی 1402
محققان گزارشات جدیدی درباره یک حمله جدید به آیفونها ارائه دادهاند که در چهار سال گذشته، هزاران دستگاه را تحت تأثیر قر…
بیشتر بخوانیداین هوش مصنوعی با تجزیه و تحلیل صدای تایپ کیبورد، قادر به تشخیص پسورد شما میباشد
- تکنولوژی و فناوری
- پویان معصومی
- شنبه, 18 آذر 1402
یک مدل هوش مصنوعی جدید از طریق میکروفون گوشی با بررسی صدای تایپ کیبورد لپتاپ، قادر به بازسازی رمز عبور کاربران میباشد.
بیشتر بخوانیدنماینده مجلس: سامانه پایش زندگی، سرک کشیدن به حریم خصوصی مردم است
- تکنولوژی و فناوری
- پویان معصومی
- چهارشنبه, 17 آبان 1402
در لایحه برنامه هفتم توسعه که روز گذشته تصویب شد، وزارت فرهنگ و ارشاد اسلامی به وظیفهای مکلف شده است. این وظیفه شامل ر…
بیشتر بخوانیدبا تصویب مجلس شورای اسلامی، سامانه رصد و پایش مستمر شیوه زندگی مردم راهاندازی میشود
- تکنولوژی و فناوری
- پویان معصومی
- سهشنبه, 16 آبان 1402
در جلسه علنی مجلس شورای اسلامی، بند "ب" ماده 75 لایحه برنامه هفتم توسعه به تصویب رسید. وزارت فرهنگ و ارشاد اسلامی به هم…
بیشتر بخوانیدقابلیت حریم خصوصی در تلگرام قویتر شد؛ جلوگیری از دریافت پیام از افرادی که در لیست مخاطبین شما نیستند
- تکنولوژی و فناوری
- پویان معصومی
- سهشنبه, 30 خرداد 1402
گاهی اوقات شما ترجیح میدهید فقط افرادی که در لیست مخاطبین شما هستند و شما شماره آنها را ذخیره کردهاید، بتوانند به شم…
بیشتر بخوانیدایمیل ۲۰۰ میلیون کاربر توییتر، به قیمت فقط ۲ دلار فروخته شد!
- تکنولوژی و فناوری
- پویان معصومی
- پنجشنبه, 15 دی 1401
طبق گزارش، دادههایی که حاوی آدرسهای ایمیل بیش از ۲۰۰ میلیون کاربر توییتر است، بهطور رایگان در فروم هکری منتشر شده اس…
بیشتر بخوانیدسامسونگ تا 2025 احراز هویت با اثر انگشت را 2.5 میلیارد برابر ایمنتر میکند
- تکنولوژی و فناوری
- پویان معصومی
- یکشنبه, 13 آذر 1401
سامسونگ ظاهراً در حال کار روی پروژهای است تا حسگرهای اثرانگشت را ایمنتر کند. یکی از این روشها میتواند جایگزینکردن …
بیشتر بخوانیداپل به اتهام جمعآوری اطلاعات کاربران با شکایت دستهجمعی جدیدی مواجه شد
- تکنولوژی و فناوری
- پویان معصومی
- دوشنبه, 23 آبان 1401
اپل به اتهام جمعآوری اطلاعات کاربران آیفون حتی در زمانی که تنظیمات حریم خصوصی این شرکت وعده داده که این کار را نکند، ب…
بیشتر بخوانیدحمله حرارتی به کمک هوش مصنوعی میتواند در چند ثانیه رمز عبور شما را برملا کند
- تکنولوژی و فناوری
- پویان معصومی
- چهارشنبه, 20 مهر 1401
متخصصان امنیت سیستمهای کامپیوتری دستگاه جدیدی ساختهاند که میتواند گذرواژه رایانهها و تلفنهای هوشمند را در عرض چند …
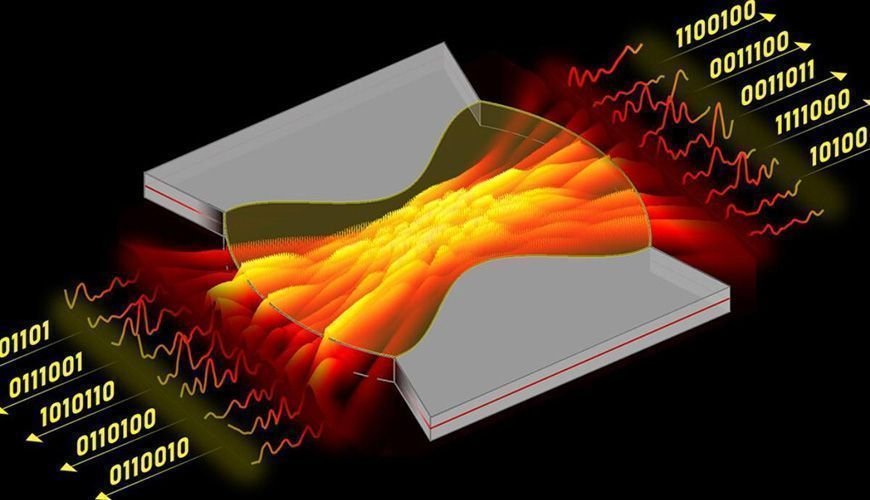
بیشتر بخوانیدمحققان چینی توانستهاند با کابل فیبر نوری، صدای افراد را از فاصله صدها متری شنود کنند
- تکنولوژی و فناوری
- پویان معصومی
- دوشنبه, 10 مرداد 1401
دانشمندان توانستهاند سیستمی طراحی کنند که صداها را در کابلهای فیبر نوری دریافت میکند و به این قابلیت را ارائه خواهد …
بیشتر بخوانیدمحققان میگویند که کره شمالی پشت حمله رمزارزی 100 میلیون دلاری بوده است
- تکنولوژی و فناوری
- پویان معصومی
- چهارشنبه, 08 تیر 1401
هفته کذشته بود که خبری اعلام شد که هکرها موفق به سرقت 100 میلیون دلاری از پل بلاکچین Horizon متعلق به هارمونی شدند. حال…
بیشتر بخوانیداحتمالا اپل و متا اطلاعات شخصی کاربران را به هکرها دادهاند
- تکنولوژی و فناوری
- پویان معصومی
- پنجشنبه, 11 فروردین 1401
گزارش جدیدی منتشر شده که در آن گفته شده کمپانی اپل به همراه متا، شرکت مالک فیسبوک در سال گذشته میلادی اطلاعات خصوصی مشت…
بیشتر بخوانیدیک هکر آمریکایی مدعی قطع کردن اینترنت کره شمالی است
- تکنولوژی و فناوری
- پویان معصومی
- جمعه, 15 بهمن 1400
در ماه گذشته اینترنت کرهشمالی دوبار قطعی داشته و وبسایتهای دولتی از دسترس خارج شده. برخی از افراد مدعی بودند که سروره…
بیشتر بخوانیدآمریکا برای پیدا کردن یک گروه هکری پاداش ۱۰ میلیون دلاری تعیین کرده است
- تکنولوژی و فناوری
- پویان معصومی
- شنبه, 15 آبان 1400
چند ماه پیش ایالت متحده اعلام کرد که با یک حمله باج افزاری روبهرو شده و خط لولهی سوخترسانی شرکت Colonial Pipeline که…
بیشتر بخوانیدسرویس توییچ هک شد؛ درآمد استریمرها به بیرون درز کرد
- تکنولوژی و فناوری
- پویان معصومی
- چهارشنبه, 14 مهر 1400
گفته میشود که این روزها تمام سرویس استریم توییچ توسط یک فرد ناشناس هک شده و اطلاعات زیادی نظیر کد منبع و اطلاعات درآمد…
بیشتر بخوانیدجوان ۲۲ ساله بریتانیایی به اتهام هک توییتر در اسپانیا بازداشت شد
- تکنولوژی و فناوری
- پویان معصومی
- پنجشنبه, 31 تیر 1400
وزارت دادگستری آمریکا مدعی شده فردی که به صورت غیر قانونی به حسابهای کاربری برخی از افراد در شبکههای اجتماعی نفوذ و ا…
بیشتر بخوانیدپاول دوروف صاحبان آیفون را برده دیجیتال نامید
- تکنولوژی و فناوری
- رسانه دیجیتال فیسیت
- شنبه, 01 خرداد 1400
پاول دوروف یکی از منتقدان همیشگی اپل بوده است. حالا گذشته از تکنولوژی ساخت آیفونها، امنیت کاربران آیفون را نشانه گرفته…
بیشتر بخوانیدسیستم لیزری بسیار سریع تولید اعداد تصادفی ساخته شد
- تکنولوژی و فناوری
- خدیجه زارعپور
- چهارشنبه, 13 اسفند 1399
اعداد تصادفی یکی از مهمترین مسائل در حوزهی امنیت و رمزنگاری است. سرعت تولید این اعداد تصادفی از اهمیت ویژهای برخوردا…
بیشتر بخوانیدبهتر است همین حالا اپلیکیشن Shareit را حذف کنید
- تکنولوژی و فناوری
- خدیجه زارعپور
- سهشنبه, 05 اسفند 1399
اپلیکیشن Shareit به واسطهی دسترسیهایی که دارد، یکی از اپلیکیشنهای خطرناک برای گوشی به حساب میآید که به گفتهی محققا…
بیشتر بخوانیدقابلیتهای امنیتی مایکروسافت اج برای امنیت بیشتر رمزهای عبور
- تکنولوژی و فناوری
- خدیجه زارعپور
- دوشنبه, 06 بهمن 1399
مایکروسافت در نسخهی مرورگر اج 88، برای افزایش امنیت پسوردهای کاربران از دو قابلیت Password Genertor و Password Monitor…
بیشتر بخوانیدترامپ در آخرین روز کاری، دستوری برای جلوگیری از حملات سایبری امضا کرد
- تکنولوژی و فناوری
- پویان معصومی
- چهارشنبه, 01 بهمن 1399
امروز آخرین روز کاری دونالد ترامپ در کاخ سفید است، حالا ترامپ دستوری را امضا کرده و خواستار اجرای آن شده، که دیگر مهاجم…
بیشتر بخوانیدحفرهی امنیتی آیفون به جاسوسها اجازه داده ۳۷ خبرنگار را هک کنند
- تکنولوژی و فناوری
- پویان معصومی
- دوشنبه, 01 دی 1399
براساس اطلاعات به دست آمده محققان متوجه شدهاند که طی یک سال گذشته آیفون خبرنگاران شبکه الجزیره به دلیل یک حفره امنیتی …
بیشتر بخوانیدجیونی 20 میلیون گوشی ارزان قیمت را به بدافزار آلوده کرده است
- تکنولوژی و فناوری
- خدیجه زارعپور
- یکشنبه, 16 آذر 1399
اینطور به نظر میرسد که شرکتهای تولید کننده گوشیهای ارزان قیمت، با نصب تروجان روی گوشی کاربران خود و نمایش تبلیغات و …
بیشتر بخوانیدهکرهای روسیه و کرهی شمالی شرکتهای تحقیقاتی کرونا را مورد حمله قرار دادند
- تکنولوژی و فناوری
- خدیجه زارعپور
- شنبه, 24 آبان 1399
بنا به ادعای مایکروسافت، سه گروه هکری با حمایت روسیه و کرهی شمالی، به هفت شرکت که در زمینهی کرونا ویروس تحقیق میکنند…
بیشتر بخوانیدباگی در ادیسون، ایمیل و محتوای ایمیلهای کاربران را فاش کرده است
- تکنولوژی و فناوری
- خدیجه زارعپور
- دوشنبه, 29 اردیبهشت 1399
ادیسون که یک برنامه ایمیل است اخیرا آپدیت شده و در این به روز رسانی کاربران متوجه شدهاند که ایمیلهای افراد ناشناس به …
بیشتر بخوانیدبه نظر میرسد شیائومی بخشی از اطلاعات خصوصی کاربران را ثبت میکند
- تکنولوژی و فناوری
- خدیجه زارعپور
- یکشنبه, 14 اردیبهشت 1399
بنا به گزارشاتی از فوربز، شیائومی دادههای کاربران هنگام وبگردی و در حتی باز کردن پوشهها و سوایپها را ثبت کرده و به س…
بیشتر بخوانیدیک باگ امنیتی خطرناک در 28 آنتی ویروس کشف شده است
- تکنولوژی و فناوری
- خدیجه زارعپور
- سهشنبه, 09 اردیبهشت 1399
محققان امنیتی ادعا میکنند بسیاری از آنتیویروسهای مشهور به باگ امنیتی خطرناکی آلوده بودهاند که باعث از کار افتادن آن…
بیشتر بخوانیدحفره امنیتی خطرناک در اپلیکیشن Mail آیفون کشف شد
- تکنولوژی و فناوری
- خدیجه زارعپور
- جمعه, 05 اردیبهشت 1399
یه حفره امنیتی خطرناک در اپلیکیشن Mail در سیستم عامل iOS کشف شده است که هکرها به واسطه آن میتوانند به آیفون نفوذ کنند.
بیشتر بخوانیدمرکز ماهر برای جلوگیری از فاش بیشتر اطلاعات کاربران وارد عمل شد
- تکنولوژی و فناوری
- سیما احمدی
- پنجشنبه, 14 فروردین 1399
به دنبال فاش اطلاعات کاربران در روزهای اخیر،مرکز ماهر خودش وارد عمل شده تا دیتابیسهای باز و حفاظت نشده را کشف کند.
بیشتر بخوانیداطلاعات 42 میلیون کاربری ایرانی تلگرام، به واسطه نسخه غیررسمی فاش شد
- تکنولوژی و فناوری
- سیما احمدی
- سهشنبه, 12 فروردین 1399
گزارشاتی نشان میدهد که به واسطه استفاده از نسخههای غیررسمی تلگرام، اطلاعات 42 میلیون کاربر ایرانی تلگرام فاش شده است.
بیشتر بخوانیدبدترین پسوردهای استفاده شده در سال 2019 کدامند؟
- تکنولوژی و فناوری
- خدیجه زارعپور
- دوشنبه, 25 آذر 1398
به رسم هر سال، لیست بدترین پسوردهای سال 2019 هم منتشر شده است. اگر شما هم از این پسوردها استفاده میکنید، هرچه سریعتر …
بیشتر بخوانیدBMW Remotely Locks Thief In Car
- تکنولوژی و فناوری
- مجتبی ذکایی
- دوشنبه, 15 آذر 1395
An alleged car thief in Seattle was caught by police after being remotely locked in a stolen BMW. The Seattle Police De…
بیشتر بخوانیدHow to enable two-step verification on WhatsApp
- تکنولوژی و فناوری
- مجتبی ذکایی
- جمعه, 21 آبان 1395
It's time to secure your WhatsApp account.
بیشتر بخوانیدUK watchdog gets Facebook to temporarily stop collecting data from WhatsApp
- تکنولوژی و فناوری
- مجتبی ذکایی
- سهشنبه, 18 آبان 1395
Facebook "pauses" WhatsApp data collection in the UK.
بیشتر بخوانیدWhatsApp under fire for sharing user data with Facebook
- تکنولوژی و فناوری
- مجتبی ذکایی
- شنبه, 08 آبان 1395
These user data stories are always interesting because half of us don’t care if one app shares our data with another, e…
بیشتر بخوانیدAndroid App Leaks Microsoft Exchange Server User Credentials
- تکنولوژی و فناوری
- مجتبی ذکایی
- جمعه, 23 مهر 1395
Android "Nine" app leaks MES user passwords
بیشتر بخوانیدApple Store fires staff for stealing customers' private pics
- تکنولوژی و فناوری
- مجتبی ذکایی
- پنجشنبه, 22 مهر 1395
The store in Australia reportedly had to bring in an HR exec to investigate.
بیشتر بخوانیدSenior Samsung official arrested for trying to sell company secrets to Chinese competitors
- تکنولوژی و فناوری
- مجتبی ذکایی
- پنجشنبه, 01 مهر 1395
Samsung is one of the largest electronics brands in the world, and it spends aconsiderable amount of capital every year…
بیشتر بخوانیدWhatsApp may soon let you protect your chats with a passcode
- تکنولوژی و فناوری
- مجتبی ذکایی
- پنجشنبه, 01 مهر 1395
Facebook-owned WhatsApp made much fanfare of the service's end-to-end encryption, which rolled out in a service-wide up…
بیشتر بخوانیدKaspersky fixes antivirus crash bug
- تکنولوژی و فناوری
- مجتبی ذکایی
- دوشنبه, 08 شهریور 1395
The denial-of-service flaws could be used to install malware.
بیشتر بخوانید3D faces based on Facebook photos can fool security systems
- تکنولوژی و فناوری
- فاطمه بهزادی
- یکشنبه, 31 مرداد 1395
Facial recognition systems aren't quite perfect yet and can still make mistakes especially when they're assessing the f…
بیشتر بخوانیدNSA classifies Linux Journal readers, Tor and Tails Linux users as "extremists"
- تکنولوژی و فناوری
- مرضیه حقیقی
- پنجشنبه, 21 مرداد 1395
Are you a Linux Journal reader or use software such as Tor and Tails Linux? If so, you've probably been flagged as an "…
بیشتر بخوانید4 signs you're a victim of ransomware
- تکنولوژی و فناوری
- فاطمه بهزادی
- دوشنبه, 18 مرداد 1395
The word ransomware conjures images of kidnappers and ransom notes. But that doesn't quite capture the reality of PC ra…
بیشتر بخوانیدMillions of Wireless Keyboards Can Let Hackers See What You're Typing
- تکنولوژی و فناوری
- مرضیه حقیقی
- چهارشنبه, 06 مرداد 1395
A newly discovered set of wireless keyboard vulnerabilities can let hachers take over your keyboard and secretly record…
بیشتر بخوانیدMaxthon browser reportedly collects sensitive data without asking
- تکنولوژی و فناوری
- مجتبی ذکایی
- دوشنبه, 28 تیر 1395
It's encrypted, but not necessarily enough to prevent info from getting out.
بیشتر بخوانیدMeet The World’s 5 Most Dangerous Child Hackers
- تکنولوژی و فناوری
- مریم بهزادی
- شنبه, 26 تیر 1395
As we all know that a hacker is someone who seeks and exploits weaknesses in a computer system or computer network. Hac…
بیشتر بخوانیدFacebook Testing End-to-End Encryption on Messenger
- تکنولوژی و فناوری
- مجتبی ذکایی
- جمعه, 18 تیر 1395
The feature will be named “Secret conversations”
بیشتر بخوانیدHalf of people plug in USB drives they find in the parking lot
- تکنولوژی و فناوری
- نگاه دیگران
- شنبه, 04 اردیبهشت 1395
A new study has found that almost half the people who pick up a USB stick they happen across in a parking lot plug said…
بیشتر بخوانیدBlackBerry signs one-year deal to provide alerts and notifications to Pentagon workers
- تکنولوژی و فناوری
- مجتبی ذکایی
- دوشنبه, 17 خرداد 1395
Just because BlackBerry has become an also-ran in the smartphone industry doesn't mean that the company isn't continuin…
بیشتر بخوانیدPatching up Web applications
- تکنولوژی و فناوری
- بختیار نیکبخت
- جمعه, 31 اردیبهشت 1395
New debugging method found 23 undetected security flaws in 50 popular Web applications.
بیشتر بخوانیدYour Instagram Photos Are Leaking
- تکنولوژی و فناوری
- مجتبی ذکایی
- شنبه, 25 اردیبهشت 1395
An installation at this year's Moogfest shows how much data the Wi-Fi on your phone is exposing about you.
بیشتر بخوانیدiPhone app can alert you if your phone has been hacked
- تکنولوژی و فناوری
- مجتبی ذکایی
- سهشنبه, 21 اردیبهشت 1395
A new app dubbed System and Security Info will scope out your iPhone for potential security threats.
Worried that your…
بیشتر بخوانیدHack The Pentagon
- تکنولوژی و فناوری
- بختیار نیکبخت
- جمعه, 17 اردیبهشت 1395
The US Department of Defence is planning a pilot of a Hack the Pentagon bug bounty program in which it will invite vett…
بیشتر بخوانیدSecurity researchers warn of key vulnerabilities in Samsung's SmartThings platform
- تکنولوژی و فناوری
- مجتبی ذکایی
- دوشنبه, 13 اردیبهشت 1395
A team of researchers from Microsoft and the University of Michigan claim to have developed attacks on Samsung's smart …
بیشتر بخوانیدWhy the Internet of Things is the next target for ransomware
- تکنولوژی و فناوری
- مجتبی ذکایی
- دوشنبه, 06 اردیبهشت 1395
Devices from pacemakers to cars could be rendered useless by ransomware infections, warns a think tank.
بیشتر بخوانیدHow You Can Get Paid To Hack The Pentagon
- تکنولوژی و فناوری
- نگاه دیگران
- پنجشنبه, 02 اردیبهشت 1395
The U.S. Department of Defense is inviting bounty-hunting computer experts to hack into the Pentagon’s website.
بیشتر بخوانیدViber joins WhatsApp and Apple with end-to-end message encryption
- تکنولوژی و فناوری
- مجتبی ذکایی
- سهشنبه, 31 فروردین 1395
Viber is adding end-to-end encryption for its users globally over the next two weeks.
Not wanting to be left behind in …
How to rescue a bricked iPhone or iPad
- تکنولوژی و فناوری
- مجتبی ذکایی
- دوشنبه, 23 فروردین 1395
Every message in WhatsApp is completely encrypted
- تکنولوژی و فناوری
- مجتبی ذکایی
- چهارشنبه, 18 فروردین 1395
Fraudsters are using you and this Ammyy of malware downloads
- تکنولوژی و فناوری
- نگاه دیگران
- یکشنبه, 15 آذر 1394
Users of Ammyy Admin may have been unwittingly downloading malware along with their remote desktop software.
A group ca…
Microsoft SmartScreen Now Protects Customers From Drive-By Attack In Edge And IE
- تکنولوژی و فناوری
- ارغوان ایاز
- پنجشنبه, 26 آذر 1394
Microsoft SmartScreen technology which is integrated with Microsoft Edge, Internet Explorer, and the Windows operating …
بیشتر بخوانیدThanks to Smartwatches, Major Universities Are Banning All Watches From Exams
- تکنولوژی و فناوری
- وجیهه نیکخواه
- دوشنبه, 23 آذر 1394
Back in my day, schools used to recommend bringing a watch into tests so you’d keep track of the time. But now, the ri…
LG's robotic vacuum is both janitor and security guard
- تکنولوژی و فناوری
- وجیهه نیکخواه
- دوشنبه, 30 آذر 1394
LG's robotic vacuum is both janitor and security guard
بیشتر بخوانیدFlash’s Farewell Under Way
- تکنولوژی و فناوری
- نگاه دیگران
- سهشنبه, 01 دی 1394
If there’s unanimity among security professionals in anything, it’s in their loathing of Adobe’s Flash Player. There’s…
Citibank is testing an ATM you can use with only your eyes and phone
- تکنولوژی و فناوری
- وجیهه نیکخواه
- پنجشنبه, 17 دی 1394
The barrier between you and your cash may be reduced drastically in the future: Citibank is currently testing a new ATM…
بیشتر بخوانید9 ways to keep your Windows computer safe
- تکنولوژی و فناوری
- نگاه دیگران
- دوشنبه, 16 آذر 1394
Monu Adaa asked for advice on staying safe in today’s crime-filled cyberworld.
For today’s criminals, the Internet’s w…
LastPass's password-shuffling rival Dashlane gets a makeover
- تکنولوژی و فناوری
- نگاه دیگران
- یکشنبه, 11 بهمن 1394
Dashlane last week unveiled a cross-platform redesign and support for five new languages with a redesign of its passwor…
بیشتر بخوانیدUbuntu's Secure Boot support vulnerability threatens even Windows PCs
- تکنولوژی و فناوری
- نگاه دیگران
- جمعه, 16 بهمن 1394
Ubuntu is thwarting Microsoft’s efforts to keep PCs safe. Modern Windows PCs are required to ship with Secure Boot enab…
بیشتر بخوانیدForget fingerprint scanners, Samsung wants to use your veins to identify you
- تکنولوژی و فناوری
- مجتبی ذکایی
- دوشنبه, 19 بهمن 1394
That’s right, Samsung has patented a smartwatch-based vein-scanning technology that would be used as a contactless alte…
بیشتر بخوانیدNew data storage solution can store the world’s data in your pocket. Forever
- تکنولوژی و فناوری
- مجتبی ذکایی
- چهارشنبه, 28 بهمن 1394
Imagine a world where you can literally store the entirety of the world’s history in your jeans pocket. Forever. Well, …
بیشتر بخوانیدFBI: Cars 'Increasingly Vulnerable' to Hacks
- تکنولوژی و فناوری
- نگاه دیگران
- سهشنبه, 10 فروردین 1395
FBI: Cars 'Increasingly Vulnerable' to Hacks
بیشتر بخوانیدUS warns against Android apps that secretly listen in on your TV habits
- تکنولوژی و فناوری
- نگاه دیگران
- سهشنبه, 10 فروردین 1395
US warns against Android apps that secretly listen in on your TV habits
بیشتر بخوانیدMicrosoft launches Azure Security Center Advanced Threat Detection, third-party tools coming in a few weeks
- تکنولوژی و فناوری
- وجیهه نیکخواه
- پنجشنبه, 06 اسفند 1394
Microsoft today announced the launch of multiple products that are meant to make companies more secure online
بیشتر بخوانیدUse Your Mac To Troubleshoot Your Wi-Fi Connection
- تکنولوژی و فناوری
- نگاه دیگران
- جمعه, 07 اسفند 1394
Want a better Wi-Fi connection on your MacBook? First you’ll want to teach yourself how wireless networks function, an…
Security and Analytics to Dominate IoT Buzz in 2016
- تکنولوژی و فناوری
- نگاه دیگران
- دوشنبه, 10 اسفند 1394
IoT is going mainstream this year, and in the rush to roll out IoT projects, IT leaders will be focused on security an…
Gmail can scan images to stop confidential data being leaked
- تکنولوژی و فناوری
- وجیهه نیکخواه
- سهشنبه, 11 اسفند 1394
Google's business platform already had the ability to scan documents, but it can now match keywords or certain text str…
بیشتر بخوانیدIoT Security Concerns Show An Industry Struggling To Keep Up
- تکنولوژی و فناوری
- نگاه دیگران
- یکشنبه, 16 اسفند 1394
IoT Security Concerns Show An Industry Struggling To Keep Up
بیشتر بخوانیدISPs Sell Your Data to Advertisers, But FCC has a Plan to Protect Privacy
- تکنولوژی و فناوری
- نگاه دیگران
- سهشنبه, 25 اسفند 1394
The Federal Communication Commission (FCC) has put forward a proposal that aims to protect Internet user's privacy.
The…
How to Use Your Phone to Detect Hidden Surveillance Cameras at Home
- تکنولوژی و فناوری
- وجیهه نیکخواه
- دوشنبه, 24 اسفند 1394
If you have reason to be suspicious of a partner or employer, or they have reason (good or bad) to be suspicious of you…
بیشتر بخوانیدHow to Use Your Phone to Detect Hidden Surveillance Cameras at Home
- تکنولوژی و فناوری
- وجیهه نیکخواه
- جمعه, 21 اسفند 1394
How to Use Your Phone to Detect Hidden Surveillance Cameras at Home
بیشتر بخوانید7 Ways Windows 10 is More Secure than Windows XP
- تکنولوژی و فناوری
- نگاه دیگران
- چهارشنبه, 09 دی 1394
Bottom line – it’s not. You can check out our Windows section for a collection of articles that will walk you through a…
بیشتر بخوانیدSamsung smart TVs will be harder to hack in 2016 with its new GAIA security solution
- تکنولوژی و فناوری
- وجیهه نیکخواه
- چهارشنبه, 09 دی 1394
Smart TVs are often written off as lacking in security, but Samsung is looking to change this. Today the company announ…
بیشتر بخوانید